Do you want to know what viruses do to a website? In this article, I will show you how websites are infected with viruses, reasons why they are there and how to remove them from there. Please read this article till the of this guide (do not rush)!
Viruses on a website are meant to steal sensitive information, disrupt functionality, redirect visitors to spam pages, completely change the website features, or even take down the website.
By default, a website is virus-free when it is initially created, however, when it starts functioning (people and bots start visiting), it will become a target of attackers to have affairs with it.
Importantly, some bots such as the ones that belong to search engines (Googlebot, Bingbot, YandexBot, Slurp) are essential for useful services like helping a website to optimize its pages (SEO), web page crawling and indexing, every website must welcome these sorts of bots. Sadly, other bots can be malicious, for example, those used for the purposes of sophisticating a website, stealing website data, disrupting indexed website pages on search results, etc.
Your work is to make sure you eliminate viruses on your website. You can have full control of bots that visit your website and also restrict people in certain locations from visiting your website if you find out that most of your attackers reside in those places. You can not have full control of your website security because you may use third-party tools such as themes, plugins, etc. which are a few of the ways that viruses can get into your website.
Now, let us get started discussing what viruses do to a website.
What viruses do to a website
1. Spamming a website’s SEO
Search engines are continually updated to detect and filter non-competent websites from their results, however, that doesn’t always remove spammed pages that are being indexed in search results.
One of the reasons viruses are injected in a website is to spam its SEO. Malicious bots and spying visitors as talked about in the introduction inject HTML code into website files or turn posts into the database itself.
If any of your web pages are being treated as described above, rather than getting rankings the way that most legitimate websites do, attackers will simply drive traffic to the content they want to rank for.
As a result of this, search results for web pages become polluted with unwanted spam keywords, as seen below.
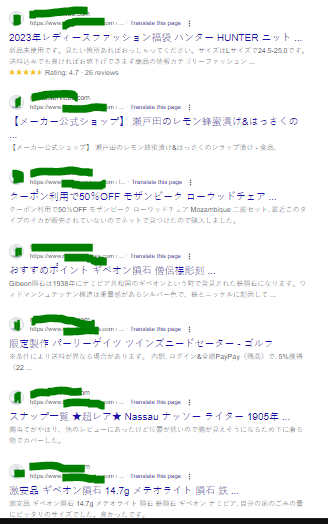
This tactic essentially allows an attacker to boost their own SEO rankings with minimal effort.
2. Redirecting
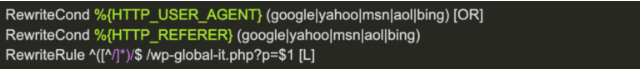
Another aim why hackers add malicious codes that later turn into viruses on a website is to redirect specific users of one website to another website. What they do is simply modify your web server configuration rules via the .htaccess or web.config files or add server-side scripts, or even include client-side JavaScript to create these malicious redirects.
You may not know when your website is redirecting your visitors to another website except a professional web manager (these attackers are very smart to not let you realize it), they regularly limit redirects to referrers or user agents to target specific visitors and avoid detection. Their intentions are often to infect your website with malware so that it gets blocklisted by search engine authorities (that is why your website does not appear on search engine results even when people type your company name).
Below is how a redirecting code looks like on a website’s .htaccess or web.config files when attackers have added a malicious code to it.
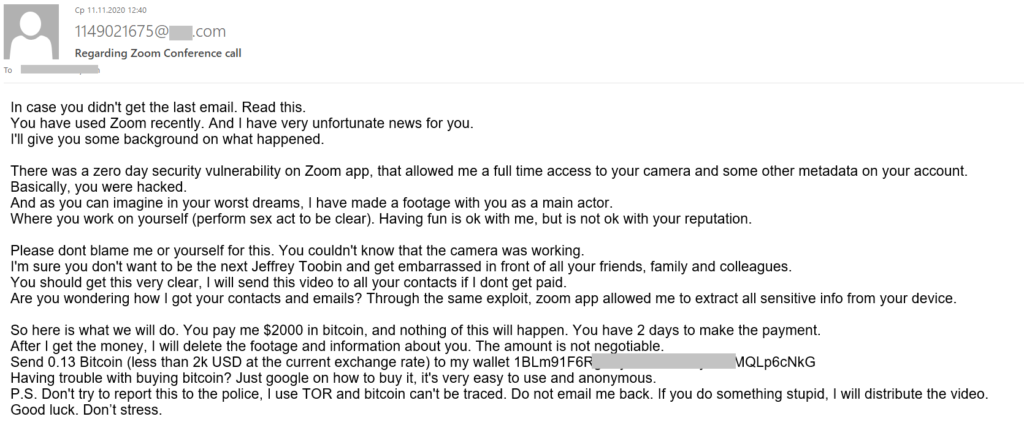
3. Phishing
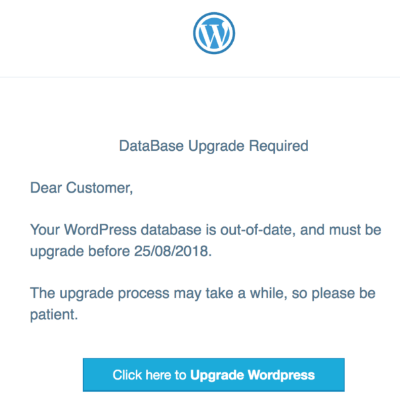
Another reason why viruses are added to a website by attackers is to trick recipients into disclosing personal or login information. They will pretend to be someone else to gain information or privileged access. Phishing campaigns can come in a variety of formats from fake login pages for reputable brands, online banking portals, landing pages for popular social networks, or even webmail portals.
What phishers do is craft login or registration pages of recognizable companies (for example, online banking portals) for victims to manipulate (convince them that they are logging into a valid service) them to enter details they might otherwise notice.
To prevent phishing issues on your website, you have to update your website database regularly. You may check our YouTube channel to watch our videos on how to update a website database.
4. Changing websites JavaScript
JavaScript is a popular programming language used extensively across the web to implement complex features on web pages. It is especially easier for attackers to compromise.
When spammers have gotten access to modify your website’s JavaScript, they first of all will try to attach their malicious code in order to trick a browser execute malware whenever the site is loaded.
These malicious JavaScript injections allow hackers to easily modify the behavior of a web page.
An example of such viruses is shown below.,
While JavaScript is only run on client side and not on the server level, it can be used to interact with a website by performing background requests. Attackers can use these requests to gather analytics about a visitor’s browser, perform actions asynchronously, or even add unwanted spam content to a web page.
5. Stealing of credit card details
By injecting malicious code on a website JavaScript, attackers can steal credit card details of the website visitors.
Attackers leverage security issues within hosting environments to infect an e-commerce website. To eliminate this, prioritize professional web developers and hosting companies to collaboratively host and develop your website so that your visitor will not be faced with security issues (downtime) as often as possible.
You may contact us for professional web development and management services we have been happily offering for years. You may see our guide on factors bloggers consider before buying a domain and hosting.
6. Enabling hack tools to work as intended
Tools that attackers use to hack or attack a website are called Hacktools. Once your website has viruses on it, it enables hackers to use their tools to easily accomplish a specific malicious goal on your website.
Hack tools don’t typically impact the website itself, they simply take advantage of server resources for malicious activities instead. For example, Distributed Denial-of-Service (DDoS) is one of the common hack tools that help to send spam emails.
Hack tools, with the aid of the presence of viruses on the website, can also be used to obtain addresses of database servers from within shared hosting environments, steal credentials from configuration files, and grab data from other configuration resources on the server.
7. Influencing back doors activities
One thing that hackers do not forget to do is add their back doors directory on a website that they compromise. Back doors a planted malicious code to allow them to easily regain unauthorized access after the initial infection.
If a virus is on your website already, attackers can easily add their back doors to it. If added, they can use remote code execution backdoor uploaders to effectively allow them to execute code using POST, GET, or COOKIE requests without a web master’s consent. Other uploaders may allow hackers to upload malicious files like spam, or hacktools to a website’s filesystem.
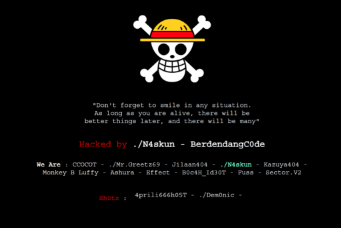
8. Defacements
New websites that are just being created mostly focused on political, ideological, or health, fraud goals, etc. use this benefit to hack existing websites in order to gain fame, have more people in their community, or share a message.
Conclusion
Hope this article has shown you a step-by-step explanation about what viruses do to a website. You may also see our guide on how to remove viruses on your website via cPanel.
If you know that this article has helped you, please subscribe to my YouTube channel for more updates. You can also follow me on Facebook.






What really causes hackers to try to hack people website? 😔 They can’t mind their business?
They should use the time they are using to try to hack and use it to develop something else that the society needs and stop defrauding people. They are very intelligent in tricking. 😔
Unfortunately, hackers do not think like that. I like your comment, dear Rose.
Naturally like your web site. I will surely come again again.
The fear of preventing a website from the activity of hackers that add viruses to websites is the beginning of wisdom (lol) 😹